Through winding mountain and then desert roads there's more than 600 miles between Aspen, Colorado and Las Vegas, Nevada. But when it comes to national security, it's the difference between the past and the future. Okay, at least the present and the future.
Aspen, a pine-scented tony Western town nestled in a valley between Colorado hills, is the home of the annual Aspen Security Forum. Usually held in late July, the event attracts the biggest names in national security, including this year the Director of National Intelligence, the heads of the CIA, NSA and National Counterterrorism Center, as well as several ex-officials who once held those posts. It's where high-level government officials, diplomats, corporate executives, veteran journalists and academic experts spar in debate on stage -- and usually make some news -- and then maybe share a quiet drink later in a dimly lit, oak-paneled bar.
It is a relatively small, quiet, respectable gathering. In the currency of national security, it is old money.
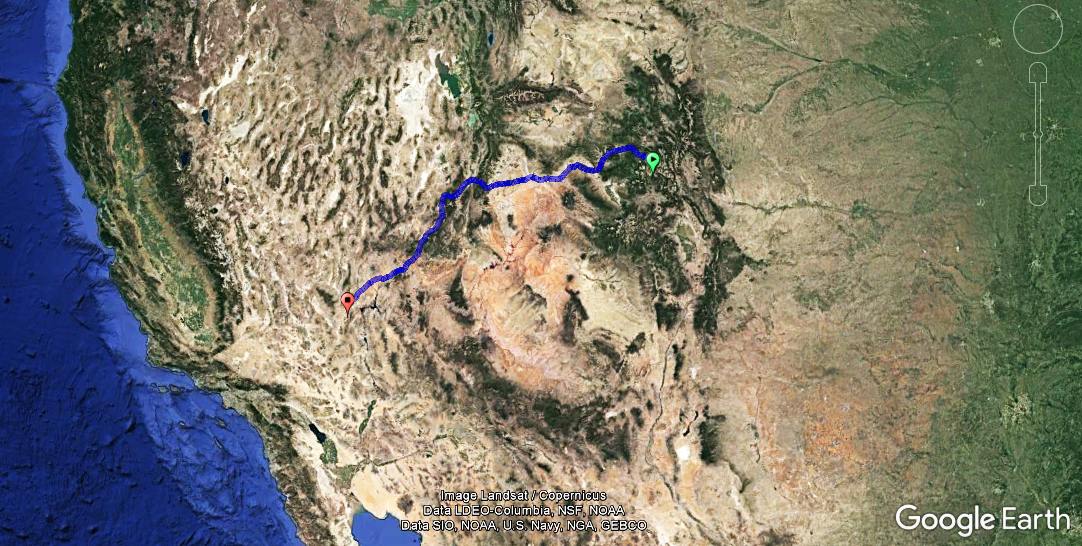
But if you're up for a road trip on the longer side, it's about a nine-hour drive, as this reporter did it last year, through some of the most beautiful land in the U.S. to where the new money is: Las Vegas.
You could fly, of course, but you'd be missing out. Taking off southwest through the mountains, passing through historical landmarks of the Old West in Grand Junction and by the rocky, alien landscape just north of Moab, eventually you'll come through Fishlake National Forest to the Nevada desert and then Sin City. There the fresh mountain air is replaced by dry oxygen pumped into the casinos, the oak-paneled bars are ditched for neon-bathed clubs and the casual refinement of the Aspen crowd is drop-kicked in favor of breaking things.
This year the Aspen forum wrapped on July 22, which was also the first training day of one of the biggest hacker conventions in the world, Black Hat. As usual Black Hat was followed by another large hacking conference, DEFCON, not to mention smaller gatherings like B-Sides -- all of which took place in Las Vegas, all full of some of the smartest people on the planet when it comes to cyber security, the latest front in the newest kind of war being fought all the time.
It was at Black Hat last year two researchers showed how they use four lines of code to exploit a vulnerability in 1.4 million vehicles that made them susceptible to digital intrusion. It was at DEFCON this year where one would have found the vote hacking village, which pitted hackers against voting machines and databases, in hopes of exposing weaknesses in the systems that could endanger the mechanism of democracy. (Spoiler alert: There were some, according to reports.)
These are the people who understand the technical details of the Russian GRU's alleged hack of the DNC, how vulnerable power grids can be and the inherent danger of the Internet of Things (IoT). It's in Las Vegas where the new generation of coders are rubbing shoulders, and they'll be the ones who will help shape the security landscape for years to come.
It's not as if this is news to the Aspen crowd. Various U.S. government law enforcement and intelligence agencies, for one example, used to be notorious for sending representatives and recruiters to the hacking conferences -- so much so that there was an annual "spot the Fed" competition. In recent years, high-level officials and ex-officials have been welcomed to the stage at Black Hat to address the ever-growing, sometimes anti-establishment-leaning audience.
Four years ago, then-NSA Director Gen. Keith Alexander became the highest-ranking U.S. official to speak at both the Aspen Security Forum and Black Hat, both times defending his agency amid the Snowden revelations.
But it's not a common trip and there's little overlap between the Aspen and Las Vegas attendees. As cyber security continues to grow in strategic importance -- not to mention often dominating the headlines -- the 634-mile journey is now one of the most crucial treks a security professional can make to get a more complete picture of the threat landscape. It's a journey from the security challenges of today, as described by revered, career professionals at the top, to the security challenges of tomorrow, as described by younger, sometimes brash hackers poking around the guts of the system.
And again, the drive is gorgeous.